Posts
Showing posts from 2017
WiFi Hacking For Beginners (Kali Linux)
- Get link
- X
- Other Apps
Hidden Ways To Get More From Your Gmail Address
- Get link
- X
- Other Apps
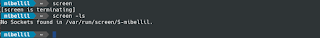
Other useful UNIX commands " history "
- Get link
- X
- Other Apps
Change the current directory [cd Command]
- Get link
- X
- Other Apps
How to Use Virtual Desktops in Windows 10
- Get link
- X
- Other Apps
How to hack a WordPress website with WPScan
- Get link
- X
- Other Apps
Best Online Cross Browser Testing Tools (Free and Paid)
- Get link
- X
- Other Apps
Honda Just Invented a Self-Balancing Motorcycle
- Get link
- X
- Other Apps
How to Hide Text in a .Text File Windows
- Get link
- X
- Other Apps
C Programming / Linux – Color Text Output (printf)
- Get link
- X
- Other Apps
Enable Super Hidden Administrator Account on Windows 7 & 10
- Get link
- X
- Other Apps
Google Chrome Manual Password Generation
- Get link
- X
- Other Apps
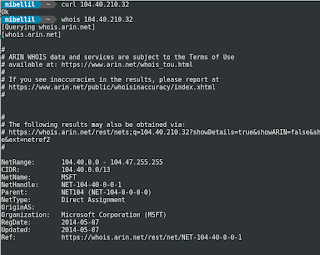
"Microsoft" Checking Internet Connection
- Get link
- X
- Other Apps
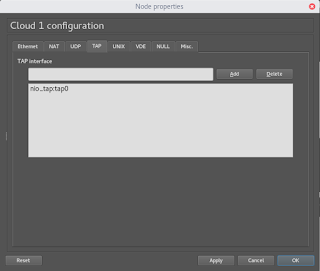
Connect GNS3 to the Internet "No ROOT"
- Get link
- X
- Other Apps
Sending raw Ethernet packets from a specific interface in C on Linux
- Get link
- X
- Other Apps